Regulations in Cybersecurity and the Role of ITSM in DORA and NIS2
Regulations in the field of cybersecurity, especially DORA and NIS2, affect a wide range of organizations. The first step in achieving compliance is typically a gap analysis, which helps assess the current state and identify the measures required to meet regulatory requirements.
Let us take a closer look at the key requirements of DORA and NIS2, their connection to IT Service Management, also known as ITSM, and how software tools can support the implementation of specific requirements.
Identification and Evaluation of Assets
Effective cybersecurity management starts with understanding what needs to be protected. This includes identifying processes, defining assets, and evaluating their importance.
An asset is anything that has value for the organization and is necessary for its operation. This typically includes data, applications, infrastructure, and services.
DORA and NIS2 use slightly different terminology and approaches, but the underlying principle remains the same. More information about asset management under the Czech Cybersecurity Act, which reflects NIS2, can be found here.
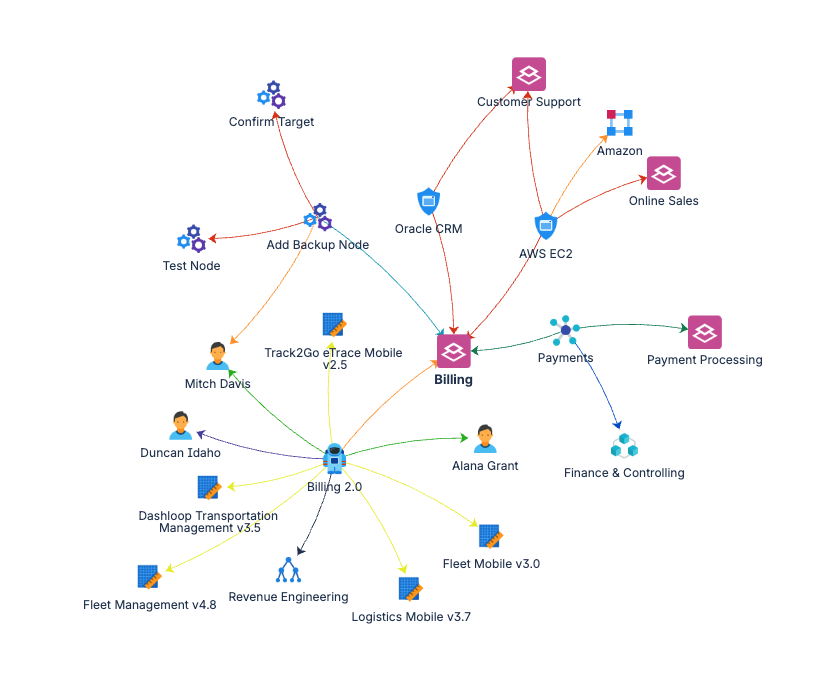
ITSM tools such as Jira Service Management provide capabilities for managing IT infrastructure and linking it to business processes. A key component is the CMDB, or Configuration Management Database, which stores configuration items such as servers, cloud services, and applications.
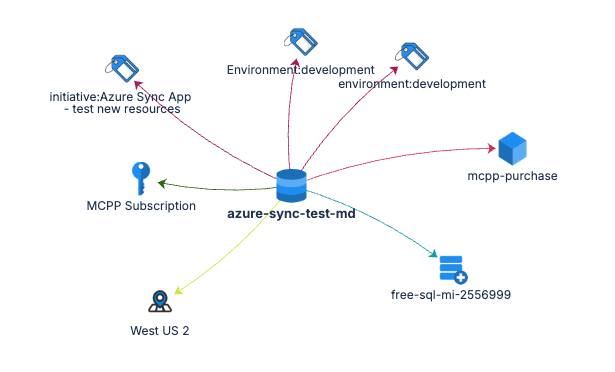
It is essential that the CMDB is complete and up to date. Ideally, updates should be automated. Organizations using Microsoft Azure together with Jira Service Management can synchronize their CMDB using tools such as Azure Sync for Jira Assets.
DORA and NIS2 approach assets from a cybersecurity perspective. These assets should be linked to the CMDB, ideally within a single system or through integration.
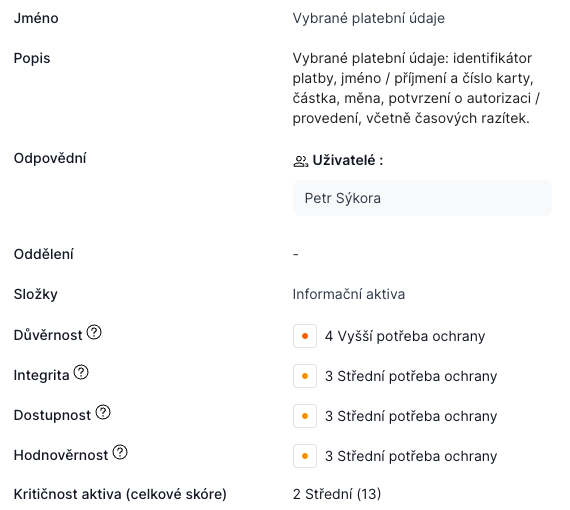
From a cybersecurity perspective, it is important not only to identify assets but also to evaluate them based on confidentiality, integrity, availability, and optionally authenticity. These parameters are used to determine the criticality of each asset.
This approach is supported, for example, by the cybreg software.
Service Portfolio and Its Link to Assets
Service Portfolio Management describes the services that an organization provides to its customers or internally.
For each service, organizations typically maintain information such as service level agreements, responsibilities and roles, and dependencies on infrastructure represented by configuration items in the CMDB.
Understanding these relationships is essential for assessing the impact of security incidents and for effective risk management.
ICT Risk Analysis and Management
One of the core requirements of both DORA and NIS2 is systematic risk analysis and management.
Once assets are identified, organizations can begin identifying and evaluating risks associated with them.
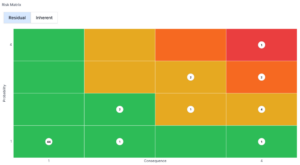
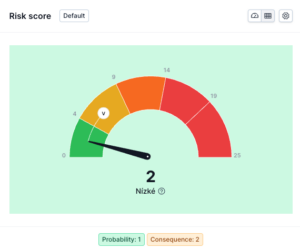
Risks are typically assessed based on asset criticality, likelihood of a threat, and potential impact. The result is a risk score that determines the appropriate risk treatment strategy.
This may include accepting the risk, reducing it through mitigation measures, transferring it for example through insurance, or eliminating it entirely.
Software solutions such as cybreg significantly simplify this process. They automate calculations, guide users through the workflow, and ensure proper documentation, which is essential for audits and demonstrating compliance.
Security Incident Management
In the event of a security incident, a fast and coordinated response is critical.
Information about an incident should be quickly captured by the service desk, where a defined process is triggered. This process includes classification of the incident, escalation to responsible teams, coordination of resolution, and tracking of regulatory reporting deadlines.
Tools such as Jira Service Management and cybreg support incident management through structured workflows, tracking, and reporting.
For example, cybreg provides predefined reports for regulatory incident reporting, making it easier to meet compliance requirements.
Recommended Tools
For implementing ITSM in modern cloud environments, we recommend Atlassian Jira Service Management. Its strengths include strong integration capabilities, flexibility, and support for the AI tool Rovo, which enables automation of many processes.
For larger organizations requiring on premise solutions, a suitable option is the combination of USU Service Management and the GRC module from Cloud Incubator.
For organizations looking for a comprehensive solution for managing cybersecurity compliance, we recommend the cybreg software. It covers policy and documentation management, asset management, risk management, incident tracking, supplier risk assessment, and regulatory reporting.
More information is available at https://www.cybreg.cz/
How We Can Help
If you are currently addressing cybersecurity or preparing for DORA and NIS2 requirements and would like to learn more, feel free to contact us.
Experts from Sykora IT and cybreg will be happy to help you design and implement a solution that meets your business needs as well as regulatory requirements.